BLOG

Arch Linux
Arch Linux is an independently developed Linux distribution (i.e. operating system) for computers based on x86-64 architecture. Composed of free and open source software, it supports community involvement. Arch Linux offers a set of scripts, while most of the other Linux distributions offer...
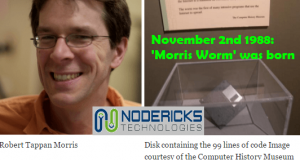
The Morris Worm story
Morris Worm (also known as the ‘great worm’ or ‘internet worm’) is the notorious computer worm which is believed to be one of the first to be distributed on the internet. It was designed by ‘Robert Thappan Morris’ and was released on ‘November 2nd 1988’, activated from a computer at MIT...
Ransomware
Ransomware is a malware designed to block access to a computing system (locking data in that system / threaten to publish the victim’s data) via encryption, until a demanded some of money is paid. As per records, ransomware variants were found as early as 1980s, demanding payments via snail...
IBM to acquire Red Hat: an overview
IBM’s announcement to acquire RedHat – the open source distribution giant – hit the headlines on last Sunday. This deal was done at a premium of more than 60% and its $34 billion price tag shook the cyber world. Due to revenue-decline for some years, IBM needed plans to efficiently boost its key...
Agent Tesla
Agent Tesla - a highly effective as well as user-friendly password stealing program which has been built using Microsoft .Net Framework and infected computers since 2014 - has gained popularity recently by having more than 6,300 customers who pay a monthly fee for subscribing its licensed version....
National Cyber Security Awareness Month (NCSAM) – October 2018
Since 2004, NCSAM has been observed in the month of October, in the United States of America (USA). NCSAM stands to encourage vigilance and protection by computer users. All of us know that in today’s IT enabled world, national security goes hand in hand with cybersecurity. NCSAM is sponsored by...
Cyber attack types to watch out for in 2018
Along with quick technical enhancements, security risks are enormous in today’s cyberspace. As per forecasts, worldwide cybercrime rates will cost 2 trillion dollars in 2019. Newer types of security threats will emerge every year. Let’s look at some of the major cyber attack types to watch...
Series on Latest Open Source Technology Trends – Topics 9 & 10
Let’s proceed to the next and, last two topics in this series. Blockchain Blockchain is a distributed digital ledger. Cryptocurrencies work upon blockchain technology. The two types of distributed ledgers are, Open (Public or Unpermissioned) – It is accessible to everyone over the network....
An effective cyber attack recovery plan for enterprises
In this digital-era of quick technical advancements, security threats are of ever-increasing concern. Cyber crime rates increase every year; so, being proactive against security risks by having an effective recovery plan in order to mitigate any loss is like a basic necessity for...